You can't afford not having this
In a 2015 Forbes online article, IBM CEO Ginni Rometty stated that cyber crime was the greatest threat to every profession, industry and company in the world. Two years later, we have yet to listen.
For years, cyber criminals have disrupted privacy, stolen personal information and proven to be a huge threat to anyone and everyone. Although the extent of the danger involved is vast and growing, it often continues to go under the radar. In today’s tech-driven world, we no longer have the courtesy of overlooking these threats or evaluating our cyber security needs. Instead, implementing procedures to ensure optimum online safety has become an urgent requirement for individuals and businesses alike.
A prime example of the capabilities of cyber crime can be seen through the history of a website called Darkode. Some have described this online marketplace as “Amazon.com for hackers,” but U.S. Attorney David Hickton once defined it as, “the largest English-speaking cyber crime forum in the world,” and “...one of the gravest threats to the integrity of data on computers in the United States.”
Darkode’s Dark History
Since at least 2008, Darkode functioned as an online store where users could trade and purchase malware and hacking tools. Members sold software that could complete invasive maneuvers like compromising cell phones. This allowed anyone willing to pay a hefty price tag to access personal cell phones and listen in on private conversations. The website also sold everything from credit card and social security numbers to email addresses and Facebook friend lists.
Over time, Darkode expanded and became increasingly used as a breeding ground for malware, botnets, viruses and more. In July 2015, after an 18-month undercover investigation, the FBI infiltrated the forum and took it down. Several months later, it re-emerged.
According to an NPR report, the Darkode takedown involved arrests in 20 countries and indictments for 70 people, 12 of whom were U.S. citizens. FBI agents spent nearly two years collecting information and evidence, and paired with Germany, the U.K., Bosnia, Serbia, Romania, India, Sweden, Denmark and Colombia among others to complete their research.
The Dark Web
Unfortunately, Darkode no longer represents the worst of what is lurking in cyberspace today. Across the world, professional hackers are using cutting-edge technologies to steal valuable information, demand ransoms and make fast, easy money. Cyber crime is occurring at bewildering rates and the dark web is thriving.
As tactics become more advanced, it becomes easier to fall victim. One current phishing scam sends Gmail users an email from a known contact with a google document attached. When they click to download the document, it takes them to a legitimate login page for Google, prompting them to log in. It asks them to authorize a “Google Docs” app to manage their emails. The app is controlled by hackers and, once activated, sends an email from the victim to all of their contacts, infecting more accounts. NYmag.com reported on this rapidly-spreading con in further detail, aiming to inform the public. Those who mistakenly fall for cyber criminal fraud, however, have to consider the true costs at stake.
Cybercrime’s Real Costs
Technological safety isn’t only a valid concern for the general public, it’s imperative for the business world as well, where the responsibility to protect client information and avoid hackers has become more critical than ever before. Failure to keep information secure not only hurts a company’s reputation, but it can also significantly impact their bottom line. According to a CSOonline article, cyber crime damage costs are predicted to hit a whopping $6 trillion annually by 2021, up from $3 trillion in 2015.
Take Action
As the government works to protect us from these threats, cyber security has to start with the individual. Protecting yourself from highly-educated, invisible cyber criminals may seem like an insurmountable task, but there are some important steps you can take to increase your security immediately.
-
Create Smarter Passwords
Most people use a lot of passwords, so they make them easy to remember, but creating simple or guessable passwords means increased risk. Passwords and security questions should not be made up of words that relate to your life. Reformed hackers have frequently said that the easiest way to attain personal and valuable information online was to find accounts with weak, predictable passwords.
Internet security professionals suggest using a mnemonic device containing the first letters of memorable words. For example, if you have a dog named Bruno who was born in 2010, instead of making your password ‘Bruno2010’, develop a sentence like, “Bruno was born in Pittsburgh in 2010.” This statement would translate into a password using the first letters and date, for example: “BwbiP2010!” (Adding a symbol of your choosing as a finishing touch makes the password even more secure).
Finally, as daunting a task as it may seem, changing the passwords to your most valuable accounts at least once every six months is highly recommended. Passwords can be developed with 2-step verification on certain systems. When this is implemented, in addition to your password, you will login with a security code that will be texted to you.
-
Don’t Overlook Key Questions
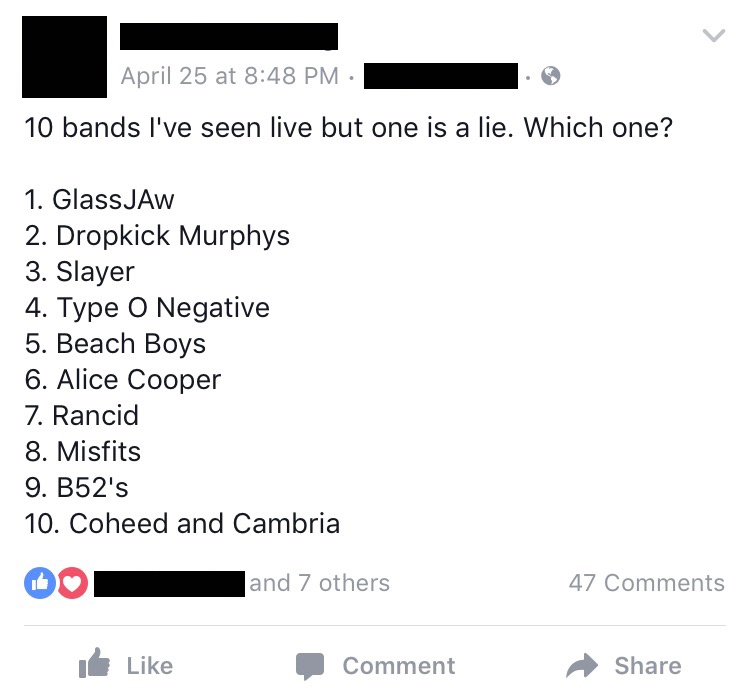
The security questions you choose are just as important as your passwords. Have you recently seen people copying and pasting a Facebook post that asks you to list 9 bands you’ve seen in concert and 1 you haven’t? The “game” is designed to have friends comment on the post to guess which concert is the “lie” (which you later reveal in the comments). There is speculation that this seemingly innocent post was developed by a hacker. Why? Because the security question to get into your email or online banking account could easily be: “What was your first concert?” or “What is your favorite band?” Never share personal information online. Even when it seems like it has no value. Every statement leaves crumbs for hackers to follow.
-
Use Safe Storage
People who create complex passwords often make spreadsheet lists to remember them all. While this can be a great organizational tool in the case of forgotten passwords, it can also put you at significant risk if your computer becomes compromised. Instead, experts suggest storing passwords on an encrypted USB key, where it can be accessed safely and privately if needed.
-
Protect Your PC - Keep your computer up-to-date with the latest software, updates and bug fixes.
Use trusted anti-virus software and make sure to renew your memberships before allowing them to expire. Cyber crime-related insurance offerings are a popular way to give your protection some significant padding. You’ve likely thought about these options for clients, but have you thought about them for yourself as well?
-
Censor Your Clicks
Take caution when clicking on links, pop-ups or email attachments. Note which websites the links wish to send you to by hovering over them before clicking, and ensuring that they are spelled correctly and not attempting to lead you to “knock-off” websites. Sometimes the only difference in the web address is ONE letter. If you are suspicious of links or attachments in emails for any reason, or if they have been sent from someone you don’t know, it’s best to avoid opening them altogether.
As cyber criminal tactics become more debilitating and evolved, it becomes more imperative that we collectively get smarter and take action. Being proactive about protecting yourself and your business online can make an incredible difference. With each day that passes, cyber crime threats grow. Prepare yourself for the dangers that lurk in the future of technology.
 |
Lindsey is a proud wife and mom with a passion for culture, travel and carbs. When she isn’t planning her next Disney cruise, she’s usually chasing her dogs, hanging with her children or anxiously awaiting another date night with her husband. |

Lindsey Elias, Marketing
As our Director of Communications, Lindsey is passionate about producing quality content. When not at the office or planning her next Disney getaway, she loves hanging with her husband, family, and fur baby and indulging in the two c's: carbs & coffee.
DISCLAIMER
The information contained in this blog post is intended for educational purposes only and is not intended to replace expert advice in connection with the topics presented. Glatfelter specifically disclaims any liability for any act or omission by any person or entity in connection with the preparation, use or implementation of plans, principles, concepts or information contained in this publication.
Glatfelter does not make any representation or warranty, expressed or implied, with respect to the results obtained by the use, adherence or implementation of the material contained in this publication. The implementation of the plans, principles, concepts or materials contained in this publication is not a guarantee that you will achieve a certain desired result. It is strongly recommended that you consult with a professional advisor, architect or other expert prior to the implementation of plans, principles, concepts or materials contained in this publication.
This blog post may contain the content of third parties and links to third party websites. Third party content and websites are owned and operated by an independent party over which Glatfelter has no control. Glatfelter makes no representation, warranty, or guarantee as to the accuracy, completeness, timeliness or reliability of any third party content. References to third party services, processes, products, or other information does not constitute or imply any endorsement, sponsorship or recommendation by Glatfelter, unless expressly stated otherwise.
Related posts
When it comes to cybersecurity, the basics can go a long way.
With so much information online—it's comforting to hear from a real person with first-hand experience with a product or service before you make a purchase.
Here are five ways you can build, expand and strengthen your professional network on LinkedIn.






Submit a Comment